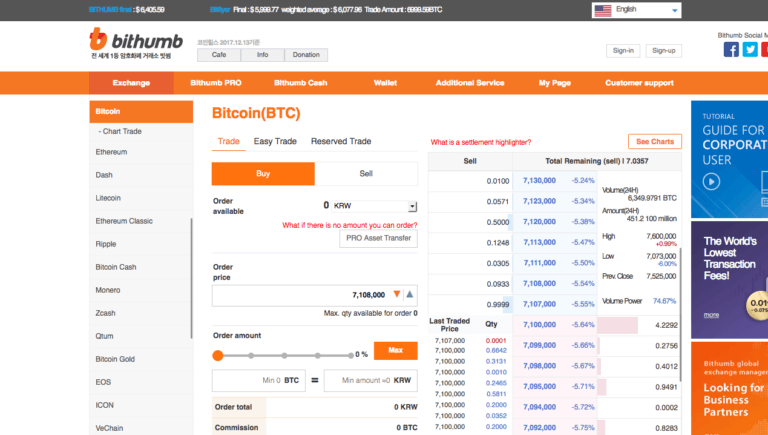
Bithumb, the world’s six largest crypto exchange (by trading volume), has been hacked, with 35 billion South Korean Won (around $31.5 million) stolen.
The South Korean exchange announced on its blog around 09:47 (Korean time) Wednesday, 20 June 2018, that it had been hacked sometime between late Tuesday night and early Wednesday morning, and that as a result of this attack, 35 billion South Korean Won, or approximately $31.5 million, was stolen.
It also told its users that all of their cryto assets were being moved to cold (offline) storage for extra security, and that until further notice, all crypto withdrawals and deposits were suspended.
The first indication that something had gone wrong came approximately an hour earlier than the above announcement, when Bithumb posted the following tweet:
[Notice for the temporary suspension of the deposits]
Due to the increasing safety issues, we are changing our wallet system.
Please do not deposit until we notify.
*All deposits are not deposited into your wallet until all changes are completed.— Bithumb (@BithumbOfficial) June 20, 2018
It then followed these with two other tweets:
*All deposit and withdrawal service will be stopped to make sure the security. We will keep notice you of the restart of the service. We apologize for your inconvenience and thanks for your understanding.
— Bithumb (@BithumbOfficial) June 20, 2018
Bithumb urgently ask our valuable customers not to deposit any fund into Bithumb wallet addresses for the time being.
— Bithumb (@BithumbOfficial) June 20, 2018
Note that none of these three tweets mentions that Bithumb was hacked. Apparently, there was another tweet that did mention that $30 million had been stolen, but that tweet appears to have been deleted.
This attack on Bithumb comes roughly 10 days after we reported that a smaller South Korean crypto exchange, Coinrail, was hacked.
We will keep you updated as the story develops.